
Dave Miller – Tech Enthusiast & Security Expert – November 30th, 2022

We all understand what tunneling literally means, but why is this phrase employed in VPNs, and if so, how is tunneling accomplished in a VPN? The primary function of a VPN is to conceal your IP address from your ISP and other outside parties. And to complete the mission, it goes through a variety of processes. Few individuals can describe how a VPN works, even though most people know what it is and how it gets utilized.
However, many don’t, and you may already be utilizing virtual private networks frequently, if not always; due to the rise in cybercrime and the need for data protection, you may now need to use it.
In a word, VPNs assist you in browsing the web safely, discreetly, and without limitations, albeit some people are still unclear about how VPNs use tunneling to accomplish this.
Keep reading this article to learn how your VPN keeps you safe and why tunneling is the only option.
As we know, a tunnel is a horizontal path through or beneath a barrier. However, it usually refers to a covered route, and the verb “to tunnel” is used. According to Merriam-dictionary, Webster’s implies creating or using a tunnel to get around a possible obstacle
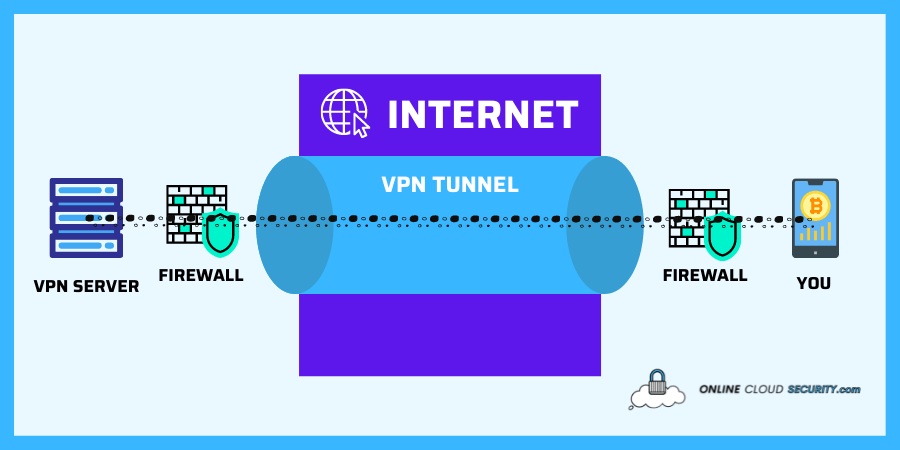
By viewing and visualizing this word, you may figuratively think that anytime it refers to a VPN, the VPN is doing something to go around a potential obstacle by making a secure pathway. And if we go into more specifics over here. Your device and a VPN server get connected in an encrypted manner. It lacks a secure key, making it hard to hack. Therefore, you are always safe from those outside the tunnel channel.
Tunnels are a way to move data across a network in networking. Therefore, consider wrapping an entire packet in another packet before it gets sent over the internet as part of the VPN tunneling procedure. The outer packet guarantees that the packet goes inside a virtual tunnel and conceals the contents from prying eyes. This outer layer of data gets removed once the packet reaches its destination, allowing access to your contents. In other words, the source and destination devices create a dedicated circuit for the duration of the connection. It prevents unauthorized parties from analyzing your data, and the packets get delivered to the intended destination.
Note: A packet in networking is a condensed version of a message or other fundamental unit of communication. Over a computer network, all data gets transferred in packets.
Although VPN tunneling is essential for securing you and your data while you are online, it cannot guarantee your data’s safety and anonymity on its own. By default, a tunnel does not offer encryption; instead, the security level gets based on the protocol that gets used. I’ll discuss this next as how is tunneling accomplished in a VPN so you may be able to increase your security at the conclusion of the article.
Although I have explained how tunneling works in VPN, here is the breakdown for steps in which few steps are generally involved.
Once you connect to the internet and use any VPN service, it starts securing your data through the set protocols of Tunneling.
To prevent unwanted parties from reading a communication, a readable message gets transformed into an unreadable form through the process of encryption. So, in VPN, the encryption method entails scrambling the data sent over the tunnel created between your VPN client and the server into an unreadable format.
VPN functions as a safe conduit between you and the internet. This tunnel is undetectable to your ISP and any outside parties.
Since it is now a two-way communication tunnel, data gets sent between your device and the internet. The data will be encrypted and decrypted as necessary by the VPN provider. And in this situation, there is a crucial idea to remember. The two-way data exchange between two networks necessitates using different protocols. Some people might be excellent at speed but poor at security, and vice versa.
As I already explained, not every VPN tunnel effectively safeguards your online privacy. A tunnel’s encryption strength might vary depending on your VPN service’s tunneling protocol. As a result, I will now describe these protocols since you know how is tunneling accomplished in a VPN.
Several VPN tunneling protocols are available, and it is up to the user to choose one. Depending on the advantages and desired conditions, these protocols have various specifications. Typically, VPN service users can modify setting to utilize the desired protocol of their choice. Some of the ones you might wish to remember are listed below.
PPTP is one of the VPN protocols that gets frequently used since it is quicker and compatible with mobile devices. Since the introduction of Windows 95 in Microsoft’s operating systems back in the 1990s, it got created by a consortium of vendors under the direction of Microsoft.
However, as VPN protocol technology has developed dramatically over the years, PPTP is quickly losing its relevance. The integrity of the tunneled data gets only weakly protected by PPTP, which is why more modern authentication techniques have replaced it. Therefore, there are many good reasons to go beyond PPTP and pick a secure protocol to safeguard your data.
L2TP has been around since 2000 and is still widely accessible. For additional security, it collaborates with another protocol, IPsec, to produce a more secure overall tunneling protocol. The L2TP/IPSec protocol typically requires two levels of authentication for data transmission; in this instance, communication is both authenticated and encrypted, is adequate in most typical usage scenarios, and has no known vulnerabilities. Despite recent research demonstrating that it shares the same vulnerabilities, it should no longer get used.
SSTP got created by Microsoft and is known as Secure Socket Tunneling Protocol, and Windows Vista established the SSTP standard first and is now in the recent upgrades of Windows. It uses 256-bit SSL keys for encryption and 2048-bit SSL/TLS certificates for authentication.
OpenVPN is more recent than SSTP, but because both VPN protocols employ SSL/TLS for encryption and the two are frequently compared. SSTP is still one of the most secure VPN protocols now available, which gets also regarded as cryptographically secure. The SSTP approach provides several benefits and drawbacks, but still, it’s safer than PPTP and more straightforward to set up.
One of the most popular open-source encryption technologies is OpenVPN. As a result, any vulnerabilities will get rapidly and easily found by the open community. It was created in 2001 as an open project, making its source available for usage and evaluation by anybody. The most effective and secure protocol currently in use is still OpenVPN. It may get set up, so internal LAN traffic and all traffic headed for the internet get routed through that tunnel.
The auto-reconnect feature of the IKEv2 protocol enhances security and usability while making the protocol quicker and more reliable. Because of this protocol, the VPN service has an instant VPN connection function that effortlessly benefits you from increased protection on wireless networks. It employs AES, ChaCha20, and Camellia 256-bit encryption for increased stability and a steady connection.
A very straightforward, quick, and contemporary VPN that makes use of encryption, WireGuard aspires to be far faster than OpenVPN. It is intended to be quickly developed with minimal code and easily auditable for security flaws. The Linux kernel and quicker cryptography used by WireGuard allow it to send data more rapidly than competing protocols.
The research process that went into creating WireGuard was protracted and labor-intensive, and each decision got given careful thought. This new VPN tunneling protocol introduction to the market looked like a breath of fresh air in VPN industry.
In summary, a VPN connects you to a distant server to conceal your location, making it impossible for anybody to track your browsing activity. An effective virtual private network may make browsing the internet securely. As a regular user, you might not always need to utilize a VPN, but for those who are more worried about security or need to get around restrictions, a VPN is the best option.
You may have a VPN that will offer you the fastest connection speed and the most reliable encryption by utilizing the many available protocols. Therefore, always seek these VPN protocols if you try to purchase a service. It will provide you with alternatives to tailor your online security.
Free software frequently fails to safeguard data and internet surfing behavior, so using it to ensure VPN security is not a good idea. Although they are few, there are some free options. You are the product if something on the internet gets offered for free. Free vpn is, therefore, against the vpn ideology. Cookies used by free VPN services might get used to customize adverts on your device, which is detrimental to your privacy and security.
**Onlinecloudsecurity.com is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a way for websites to earn advertising revenues by advertising and linking to Amazon.com and affiliated sites. As an Amazon Associate we earn affiliate commissions from qualifying purchases.**

Dave Miller is an IT Consultant for Online Cloud Security and has over 7 years of experience in the Information Technology space. He also specializes in repairing laptops & computers. In his spare time, he loves to talk about new technologies and hosts monthly IT and Cyber Security meetings in the Houston area.
Click any button down below to share this article on the following channels:
Online Cloud Security is here to recommend you the most secure devices, from laptops to smartphones, we only want to provide you with products that we have tested and used ourselves for online security. Every product that we recommend is heavily inspected and tested for security against hackers, viruses, malware, and any other intruders that may want to steal your information.
Online Cloud Security is here to recommend you the most secure devices, from laptops to smartphones, we only want to provide you with products that we have tested and used ourselves for online security. Every product that we recommend is heavily inspected and tested for security against hackers, viruses, malware, and any other intruders that may want to steal your information.
Your Trusted Source for Online Security