
Dave Miller – Tech Enthusiast & Security Expert – November 13th, 2021

The cryptocurrency hype is not new, virtually currency is the current economic trend. As every technology has some rules to be used in a protected manner likewise is the case with cryptocurrency. This is a virtual currency and after the pandemic situation, it has gained more popularity.
However, the recent virtual halt and sluggish economic growth have prompted the dire need for secured cryptocurrency trading. So, have you ever come across the situation when you warn someone from using bank details online, we all have had such experiences that are justified fear of being robbed through online hacking systems.
In the case of cryptocurrency, it is itself is a virtual currency that is traded online therefore fear of its being hacked and stolen is very possible, according to BBC, Liquid, a Japanese cryptocurrency exchange got almost $100 million worth of crypto stolen from hackers. With this said, should you use a VPN for trading crypto securely?
VPN stands for Virtual Private Network, it is a network that uses certain protocols to route the data in the most efficient and protected manner. It provides a secure tunnel between the user device and the internet thereby protecting the user of cryptocurrency a haven to trade in secured from any kind of snooping or interference.
How unrealistic the situation seems when somebody leaves their money open on the roadside and expects it to be safe. The absence of VPN is just like this, in the case of cryptocurrency trading one cannot be on the sure footing to be on the safe side from crypto-jacking (hacking) or cryptocurrency being misused because there are no security arrangements.
A VPN (Virtual Private Network) is the most effective way to protect internet traffic as it encrypts the data as soon as the subject device is connected to the VPN server. The data is encrypted in such a manner that nobody can see into it be it the hacker, government officials, or even the internet service provider. Moreover, it changes the IP address which shows as anonymous when tried to be tracked.

VPN indeed provides a secured shield for working and dealing with protection however, it does not assure 100% security. Therefore, options such as anti-virus, hardware wallets, script blockers, and password managers must also be used. Although this is an acknowledged fact that a good VPN assures the security of currency along with data as it encrypts that data and re-routes it as well which shows the user as anonymous.
VPN (Virtual Private Network) provides a secured data passage and when it comes to dealing in the virtual currency it is one of the most encouraging things to keep people safe from being robbed off. Therefore, the legality of VPN is verified by most countries. However, the legality of VPN by no means assures illegal online trading, that is to say, that if the cryptocurrency is used for some illegal purpose then that purpose cannot be counted in the circumference of legality by any means.
A VPN is expected to slow down the internet connection as well as drain the battery of the device. If the internet connection is observed to be slowed after VPN it is generally advised to use the connection of server that is closest in geographical terms. And when it comes to drainage of battery it is obvious fact that each app increases the usage of battery and VPN is no exception to that fact.
Phishing is the way of online stealing that is used by hackers. This is the way how they get to the cryptocurrency assets and take them away. It is generally proceeded by sending some link to the device and the moment that link is clicked on or some data is entered on the said link, it gives the hacker way to reach to cryptocurrency asset. This is how the hackers steal the assets. However, when VPN is used it gives safe passage of data and does not allow any such attempts to reach the system. Therefore, there are the least chances of being vulnerable through this procedure.
IP stands for Internet Protocol. It is the unique address that is associated with each device on the internet or a local network. When the VPN (Virtual Private Network) is used it hides the IP address of the subject device. This shows that the device is anonymous on the system that makes it approximately impossible for the hacker to hack the system and get way to cryptocurrency assets.
VPN (Virtual Private Network) encrypts the data in such a manner that only desired device can decrypt the information. The VPN provides a secured tunnel between the attached device and the internet that keeps the content of cryptocurrency completely private. The data which is not in readable form cannot be used in a harmful manner. So, VPN secures the cryptocurrency as all the data that is regarding the currency is not accessible to any third party.
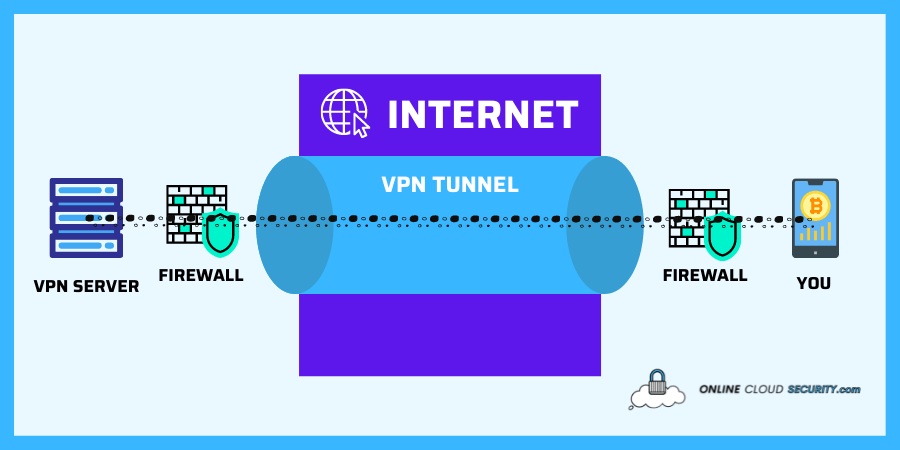
VPN Tunneling is one of the data protection methods while using VPN along with encryption. The process of tunneling secures the cryptocurrency assets’ data from being leaked and misused by a third party. The cryptocurrency is secured within an online tunnel kind of security that saves it from being theft or leaked.
So, VPN gives a secured passage to cryptocurrency. As the word suggests the tunneling keeps the outsiders away even from the shadow of those who are having a safe passage under the tunnel. Throughout this tunneling process, one cannot put enough emphasis on the fact that cryptocurrency assets are safe and secure. This tunneling is subject to encryption and change of location. These are the two things that jointly form a tunnel or the soldiers or weapons in the tunnel.
VPN also gives the option of a change of location. This trick is to trap the hackers. The IP address is a unique address to identify the device on the internet. With VPN one can change the location to whichever country one selects. So if the user selects London, japan, china, or any other state it will appear accordingly. So the hacker won’t be able to get the actual location of cryptocurrency assets. This is how VPN secures cryptocurrency trading. It is obvious fact that when a hacker will have no information regarding the location of the asset how can there be any possibility for a hacker to steal the asset.
Authentication is a process that means establishing a secure connection between server and client of VPN. This is a critical process that takes time to establish which is the installing or setting up process. Once the authentication of the network is done. VPN reassures that all cryptocurrency assets are safe and secure. The cryptocurrency cannot be used by any third party through malicious means. So this is also one of the reasons that VPN must be used for the security of virtual monetary assets.
The server location must be kept into consideration while purchasing a VPN. When dealing with cryptocurrency the expected targeted marketing is the whole world. So the VPN should have worldwide access this will expand the trading opportunities concerning cryptocurrency, as there will be VPN protection worldwide no one would be ever able to track the user of cryptocurrency back. Therefore, geographical access of the server, as well as the server location, must be kept into consideration in first and foremost priorities.
As the market of VPN is huge therefore it is incumbent upon the user to pick the best available option in this regard. The VPN is capable of keeping the logs which keeps the track of all the data usage and the websites that have been contacted for cryptocurrency trade make the monetary assets vulnerable from being stolen.
When VPN is keeping the log it means that the internet service provider does not have any access to the cryptocurrency data but the VPN provider does have all the data which renders the user again vulnerable to being robbed off. Therefore, the best option in this regard is to choose a VPN that does not keep track of logs. The VPN provider who aims at securing the data of their client gives this no log option. So this is the actual checkmark to know which VPN should be selected for the protection of cryptocurrency assets.
VPN provides secured passage for the data and cryptocurrency is virtual money that needs online security from hackers. Therefore, the usage of VPN for cryptocurrency is much appreciated. It not only secures the cryptocurrency assets but also increases the confidence of trading in cryptocurrency. As the sense of security is the first and foremost requirement of any sort of business.
**Onlinecloudsecurity.com is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a way for websites to earn advertising revenues by advertising and linking to Amazon.com and affiliated sites. As an Amazon Associate we earn affiliate commissions from qualifying purchases.**

Dave Miller is an IT Consultant for Online Cloud Security and has over 7 years of experience in the Information Technology space. He also specializes in repairing laptops & computers. In his spare time, he loves to talk about new technologies and hosts monthly IT and Cyber Security meetings in the Houston area.
Click any button down below to share this article on the following channels:
Online Cloud Security is here to recommend you the most secure devices, from laptops to smartphones, we only want to provide you with products that we have tested and used ourselves for online security. Every product that we recommend is heavily inspected and tested for security against hackers, viruses, malware, and any other intruders that may want to steal your information.
Online Cloud Security is here to recommend you the most secure devices, from laptops to smartphones, we only want to provide you with products that we have tested and used ourselves for online security. Every product that we recommend is heavily inspected and tested for security against hackers, viruses, malware, and any other intruders that may want to steal your information.
Your Trusted Source for Online Security