
Dave Miller – Tech Enthusiast & Security Expert – February 5th, 2022
Blockchain Can Be Hacked. It is possible to compromise a blockchain. While blockchains used to be considered a “unhackable” technology that powered and protected cryptocurrencies, this no longer holds true, as evidenced by recent events.
By exploiting the unique weaknesses of blockchains, blockchain has been hacked roughly $2 billion in cryptocurrencies since 2017. That is to say, don’t believe the hype about the security of Bitcoin’s blockchain. It is no safer than any other method of storing data. Ethereum Classic’s network was taken over by a hacker who was able to change transaction history. By exploiting “double-spending,” the attacker made off with $1.1 million worth of digital currency.
Nowadays we know that blockchain can be hacked in many ways. A blockchain is a digital ledger that is constantly being updated by a distributed network of computers. A blockchain protocol is a collection of rules that govern how the computers in the network, known as nodes, validate and record new transactions.so the important thing is has blockchain ever hacked. It uses encryption, game theory and economics to encourage nodes to work toward the network’s security rather than attack it for financial benefit. False transactions can be exceedingly difficult and expensive to add, but real ones can be easily verified if the system is properly configured.
As a result, the technology has attracted the attention of a wide range of businesses, including finance. Financial giants like Fidelity Investments and Intercontinental Exchange, owner of the New York Stock Exchange, are preparing to introduce new services that will integrate blockchains into the existing financial system in the coming months. Even the nation’s central banks are considering using them to create new digital currency.
However, the more difficult it is to set up a blockchain system, the more opportunities there are for mistakes to occur. A “subtle cryptographic weakness” that had been mistakenly baked into the Zcash protocol was covertly rectified earlier this month, according to the corporation in charge of the cryptocurrency. Zcash uses incredibly complicated math to allow users to deal privately. In theory, an attacker might have used it to create an infinite supply of fake Zcash. No one appears to have actually attempted this.
Because of this, it’s important to keep in mind that cryptocurrencies can’t completely avoid the flaws of traditional financial systems, even if they’ve received a lot of attention recently. The venues where people trade and retain cryptocurrency were the usual targets for hackers prior to the attack on Ethereum Classic. As explained by MIT Tech how the blockchain has been hacked, the hacker was able to cheat other users by acquiring control of the digital currency’s computational power and then modifying the existing blockchain ledger to mask their tracks. The so-called “51 percent attack” uses this new ledger as the official one.
Smaller coins are easier to take over than larger cryptocurrencies, but it’s still a costly trick to pull off. Furthermore, we should expect to see many more 51 percent attacks in the near future. There are still many phishing and virus attempts that take advantage of naive victims by convincing them to hand over their passwords.
Not only does the protocol itself need to be protected, but so does everything else involved. You need a software client to trade cryptocurrencies or run a node if you want to do so independently. This software client, however, may contain security flaws. In September, Bitcoin Core developers scrambled to address a flaw (also secretly) that may have allowed attackers to generate more bitcoins than the system is designed to allow. Bitcoin Core is the main client for Bitcoin.
Most cryptocurrencies are vulnerable to a 51 percent attack. Blockchain can be hacked by this way. There is a reason for this: Blockchains that use proof of work as their verification protocol are the majority of the time. Nodes use enormous amounts of computer power in this process, which is also known as mining, to establish their trustworthiness before they may add new transaction data to the database. It’s possible for a miner to scam other users by sending them payments and then producing an alternate version of the blockchain in which the payments never occurred. A fork is the name given to this new iteration. If the attacker has control of the majority of the mining power, he or she can make the fork authoritative and proceed to spend the same bitcoin.
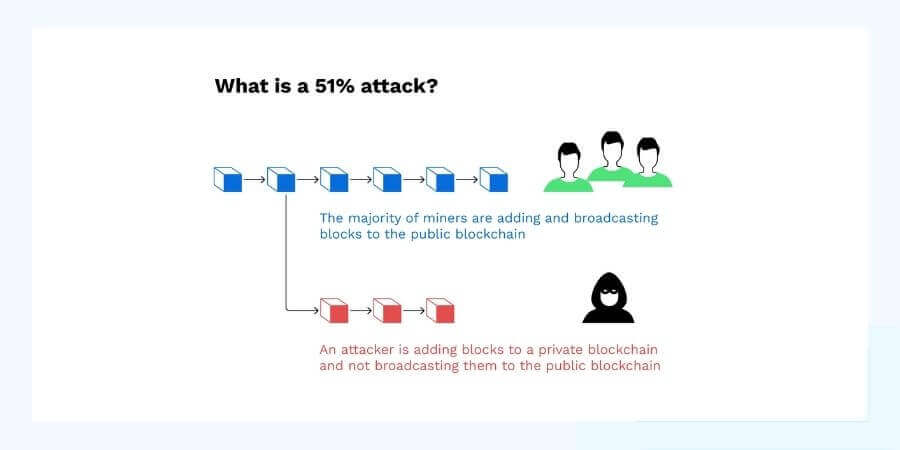
An attempt at such a robbery will almost certainly be prohibitively expensive on popular blockchains. Renting enough mining power to attack Bitcoin costs more than $260,000 per hour. There are more than 1,500 cryptocurrencies to choose from, and the cost of each decreases as you get further down the list. Because miners turn off their devices when the price of the coin drops, the network becomes less secure.
Around the middle of 2018, hackers began launching 51 percent assaults on a number of smaller, less widely traded coins, including Verge, Monacoin, and Bitcoin Gold, stealing an estimated $20 million in value in the process. Vertcoin was the target of a series of attacks in the fall that resulted in the theft of around $100,000. To our knowledge, this was the first time an attack on a top-20 currency had been successful.
As the number and intensity of 51 percent attacks rises, the exchanges will bear the brunt of the financial harm caused by double-spends, according to David Vorick, cofounder of the blockchain file storage platform Sia. According to him, the growth of so-called hashrate markets, where attackers can rent computer power for assaults, has been one factor driving this trend. After the Ethereum Classic attack, Vorick commented, “Exchanges will need to be considerably more conservative when deciding which cryptocurrencies to support.”
In the development of a blockchain, security flaws or errors may occur. With increasingly complex blockchains, this may happen more frequently. It’s possible to discover the weaknesses and attempt an attack when this happens. Smart contracts, which function on a blockchain network, have experienced this. Smart contracts can be used for a variety of purposes, including facilitating financial transactions and automating tedious chores.
When working with clients and cases, lawyers may come into contact with smart contracts as a result of their work. Due to the fact that fraudulent behavior isn’t recorded on the blockchain network, hackers could take money from users without being caught if a security weakness exists. Because of the immutability of blockchain transactions, the only way to recover lost funds is to create a fork that is universally recognized as the official chain.
In addition to 51 percent attacks, researchers are just beginning to study the ramifications of a new level of blockchain security weaknesses like “how blockchain has been hacked?”. Ethereum Classic—specifically, its founding story—coincidentally serves as an excellent foundation for comprehending them as well.
It is computer software that runs on a blockchain network called a “smart contract”. Automated movement of cryptocurrency can be done with this tool. Uses like facilitating real legal contracts or complex financial transactions could benefit from this technology. Another use—and the one that we’re focusing on—is the creation of a voting mechanism that allows all of the participants in a venture capital fund to collectively select how the money is allocated.
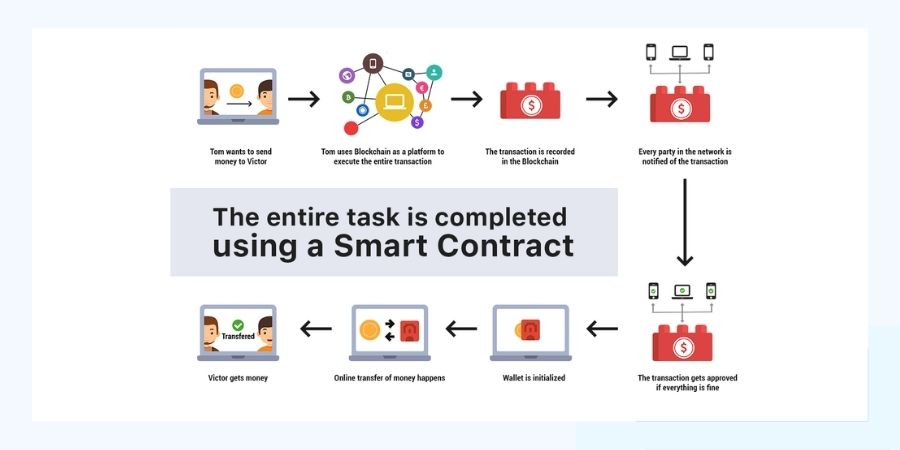
In 2016, the Decentralized Autonomous Organization (DAO), a blockchain-based fund, was established. A short time later, an attacker exploited a previously unknown hole in a smart contract governing the DAO to steal more than $60 million in Ethereum. That bug allowed a hacker to repeatedly request funds from accounts even though the system had already detected an earlier withdrawal.
A defect in a live smart contract, as demonstrated by the hack, can cause a unique kind of emergency. Patches are the traditional means of fixing bugs in software. In the blockchain world, things aren’t as straightforward as they appear to be at first glance. According to Petar Tsankov, a research scientist at ETH Zurich and cofounder of a smart-contract security business called ChainSecurity, deploying a smart contract is like launching a rocket because blockchain transactions cannot be undone. It’s impossible for the software to make an error.
Fixes can be found, to some extent. It’s not possible to modify or add new functionality to contracts, but they can be “upgraded” by adding new smart contracts that interact with the existing ones. If a hack is found, developers can also embed kill switches into the network so that all activity is halted. However, for those who have already had their money taken, it is too late.
In order to get the money back, the blockchain must be reset to a point before the blockchain hacking attempts occurred, a fork must be created, and everyone on the network must agree to use that new blockchain instead. That was the decision of Ethereum’s developers. Ethereum, as it is now commonly known, was adopted by the vast majority of the community, but not everyone. The original Ethereum chain, known as Ethereum Classic, was maintained by a limited group of supporters.
There has been a dramatic spike in the number of blockchain attacks recently; as hackers have realized that the system is vulnerable. Most of the time through the vulnerable system blockchain has been hacked. Hackers have gotten away with $2 billion in blockchain cryptocurrencies since 2017, according to data made available to the public. Users should exercise caution when trading on exchanges, especially in light of the current hacking activity.
If you’re a lawyer who deals with blockchain, it’s important to stay up to date on the risks and potential solutions. Prior to use smart contracts or trading on an exchange, make sure you study any prior attacks and any applicable security precautions that may exist. There is no need to be overly concerned at this point, as the design of the blockchain is still quite secure but blockchain can be hacked like other sites. Security measures will undoubtedly be improved in the future by developers and administrators.
**Onlinecloudsecurity.com is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a way for websites to earn advertising revenues by advertising and linking to Amazon.com and affiliated sites. As an Amazon Associate we earn affiliate commissions from qualifying purchases.**

Dave Miller is an IT Consultant for Online Cloud Security and has over 7 years of experience in the Information Technology space. He also specializes in repairing laptops & computers. In his spare time, he loves to talk about new technologies and hosts monthly IT and Cyber Security meetings in the Houston area.
Click any button down below to share this article on the following channels:
Online Cloud Security is here to recommend you the most secure devices, from laptops to smartphones, we only want to provide you with products that we have tested and used ourselves for online security. Every product that we recommend is heavily inspected and tested for security against hackers, viruses, malware, and any other intruders that may want to steal your information.
Online Cloud Security is here to recommend you the most secure devices, from laptops to smartphones, we only want to provide you with products that we have tested and used ourselves for online security. Every product that we recommend is heavily inspected and tested for security against hackers, viruses, malware, and any other intruders that may want to steal your information.
Your Trusted Source for Online Security